Escalating threats
Over 68% of firms suffered recent attacks and 80% were unknown “zero-day” threats.
Enterprise-class threat detection, isolation, and
remediation for Windows and Mac
Over 68% of firms suffered recent attacks and 80% were unknown “zero-day” threats.
Sources: 2020 EDR Study, Ponemon Institute
Almost 60% of firms need zero-day detection, but high false positives are a key concern.
More than 61% of firms say complexities and limited staff are significant EDR challenges.
Sources: 2020 EDR Study, Ponemon Institute
Detection and protection against ransomware, malware, trojans, rootkits, backdoors, viruses, brute force attacks, and “zero-day” unknown threats.
Detection and protection against ransomware, malware, trojans, rootkits, backdoors, viruses, brute force attacks, and “zero-day” unknown threats.
Malwarebytes Endpoint Detection and Response for Windows and Mac can easily replace or augment other endpoint security solutions, including Microsoft Defender.
Malwarebytes EDR uses unique Anomaly Detection machine learning to not only detect known threats, but also find unknown “zero-day” threats.
Malwarebytes EDR offers remote worker optimization, industry-leading efficiency, high return on investment (ROI), and low total cost of ownership (TCO)
Higher Remote Desktop Protocol (RDP) usage resulting from the COVID-19 pandemic have exposed an exploitable vector for ransomware.

Malwarebytes Endpoint Detection and Response now includes Malwarebytes Brute Force Protection to block malicious login attempts and prevent intrusion attacks targeting RDP on Windows workstations and servers.
Our powerful scan and detection engine provides stronger protection against infections from exploits and packaged and polymorphic malware, making it ideal for remote work environments where users may be easier targets.

Sophisticated attacks exploit entry points and security holes, and once attackers are inside, they can set hooks that cause serious damage.

Malwarebytes Endpoint Detection and Response now includes improved enterprise-class detection that leverages our anomaly detection machine learning technology. “Zero-day” detection has been enhanced to find and stop unknown threats.
Obfuscated malware can cleverly bypass traditional EDR. Our expanded detection capabilities catch these threats, and our enhanced behavioral detection alerts on anomalies in user behaviors.

The average enterprise security team spends over 25 percent of their time chasing thousands of false positive alerts each month (Ponemon).

Malwarebytes Endpoint Detection and Response solves this problem by ensuring an optimal balance between high effectivity with our advanced anomaly detection and low false positives alerts.
New U.S. and international compliance mandates now require more stringent protection of Personal Information (PI). Firms may only have small windows to prove that alerts did not expose PI or they could be fined, forced to publicly announce, and be sued for millions.

Higher Remote Desktop Protocol (RDP) usage increases resulting from the COVID-19 pandemic have exposed an exploitable vector for ransomware.
Malwarebytes Endpoint Detection and Response now includes Malwarebytes Brute Force Protection to block malicious login attempts and prevent intrusion attacks targeting RDP on Windows workstations and servers.
Our powerful scan and detection engine provides stronger protection against infections from exploits and packaged and polymorphic malware, making it ideal for remote work environments where users may be easier targets.
Sophisticated attacks exploit entry points and security holes, and once attackers are inside, they can set hooks that cause serious damage.
Malwarebytes Endpoint Detection and Response now includes improved enterprise-class detection that leverages our anomaly detection machine learning technology. “Zero-day” detection has been enhanced to find and stop unknown threats.
Obfuscated malware can cleverly bypass traditional EDR. Our expanded detection capabilities catch these threats, and our enhanced behavioral detection alerts on anomalies in user behaviors.
The average enterprise security team spends over 25 percent of their time chasing thousands of false positive alerts each month (Ponemon).
Malwarebytes Endpoint Detection and Response solves this problem by ensuring an optimal balance between high effectivity with our advanced anomaly detection and low false positives alerts.
New U.S. and international compliance mandates now require more stringent protection of Personal Information (PI). Firms may only have small windows to prove that alerts did not expose PI or they could be fined, forced to publicly announce, and be sued for millions.
If an endpoint is attacked, you can easily halt malware from spreading and causing harm.

Network isolation limits device communications, so attackers are locked out and malware can’t “phone home.” Process isolation estricts which operations can run, halting malware while still allowing end users to work away.
Desktop isolation alerts the end user of the threat, temporarily blocks their access, yet keeps the device online for analysis.
With multiple modes of attack isolation, both security teams and end-users maximize their productivity even during attacks.

Find and reverse all major and subtle changes made by malware.

While traditional approaches focus on removing only the active executable, they ignore residual change that leads to re-infection or pesky PUPs and PUMs. You’re then left to reimage the device, or hope for the best.
Quite the opposite, the proprietary Malwarebytes Linking Engine tracks every artifact, change, and process alteration (including memory executables others miss). A true “one and done” solution, it then maps out the correct path to remove all malware permanently, including PUPs and PUMs.

For Windows environments, paying ransomware is no longer a requirement.

It’s possible because we make use of local cache on each endpoint, storing all relevant changes to the device for up to 72 hours. If you’re infected, Malwarebytes simply backs out device changes and restores files that were encrypted, deleted, or modified. And data storage space isn’t an issue, as our proprietary dynamic exclusion technology learns “good” behavior of applications and minimizes storage utilized.
The result is peace of mind knowing that ransomware won’t damage your bottom line, reputation, customer experience, or team productivity.

If an endpoint is attacked, you can easily halt malware from spreading and causing harm.
Network isolation limits device communications, so attackers are locked out and malware can’t “phone home.”
Process isolation restricts which operations can run, halting malware while still allowing end users to work away.
Desktop isolation alerts the end user of the threat, temporarily blocks their access, yet keeps the device online for analysis.
With multiple modes of attack isolation, both security teams and end-users maximize their productivity even during attacks.
Find and reverse all major and subtle changes made by malware.
While traditional approaches focus on removing only the active executable, they ignore residual change that leads to re-infection or pesky PUPs and PUMs. You’re then left to reimage the device, or hope for the best.
Quite the opposite, the proprietary Malwarebytes Linking Engine tracks every artifact, change, and process alteration (including memory executables others miss). A true “one and done” solution, it then maps out the correct path to remove all malware permanently, including PUPs and PUMs.
For Windows environments, paying ransomware is no longer a requirement.
It’s possible because we make use of local cache on each endpoint, storing all relevant changes to the device for up to 72 hours. If you’re infected, Malwarebytes simply backs out device changes and restores files that were encrypted, deleted, or modified. And data storage space isn’t an issue, as our proprietary dynamic exclusion technology learns “good” behavior of applications and minimizes storage utilized.
The result is peace of mind knowing that ransomware won’t damage your bottom line, reputation, customer experience, or team productivity.
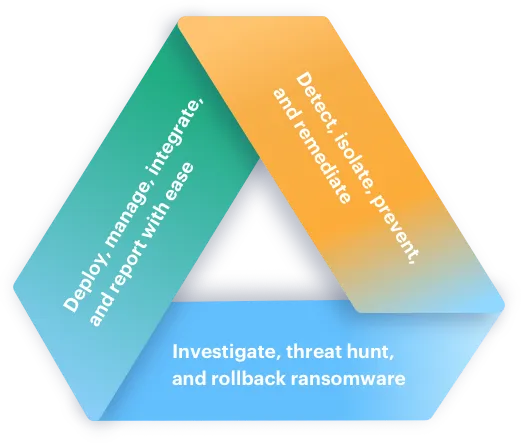
With a few simple clicks you can protect your business and brand, improve your regulatory compliance posture, and avoid costly downtime. Malwarebytes Endpoint Detection and Response for Windows and Mac offers enterprise-class endpoint protection, advanced threat hunting, and reliable isolation, remediation, and response to cybersecurity attacks.
Customers have spoken, and Malwarebytes is highly rated. Read what fellow security professionals say about us and why we are named a Customers' Choice.

Source: Gartner, Gartner Peer Insights ‘Voice of the Customer’: Endpoint Detection and Response Solutions, Peer Contributors, 1 May 2020. This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from Malwarebytes.
“We know we have confidence that if we do get ransomware, we have the ability to roll back up to 72 hours per endpoint.”
Robert Elworthy
Assistant Director of IT, Langdale Industries
Join the community of more than 60,000 Malwarebytes enterprise customers that have built their endpoint resilience.
Select your language